 Put frankly, it has been a scary couple days to start 2018 when it comes to computing in general. If you’ve been around basically any tech site on the internet, you’ve likely come across the latest mega-issue plaguing what seems to be every device on the planet.
Put frankly, it has been a scary couple days to start 2018 when it comes to computing in general. If you’ve been around basically any tech site on the internet, you’ve likely come across the latest mega-issue plaguing what seems to be every device on the planet.
The bad news? It’s incredibly widespread. The good news? Your Chromebook may already be patched and has the ability to employ a new feature that will help mitigate your vulnerabilities. Let’s talk through a couple things you need to know with regards to your Chrome device, Meltdown, and Spectre.
What Is This, Exactly?
Let me make this incredibly clear: I don’t possess the deep understanding and expertise to fully explain what is happening on a deeply technical level. I can give you a quick overview and will provide a few articles for your consumption written by people who are far more intimate with the nitty, gritty details.
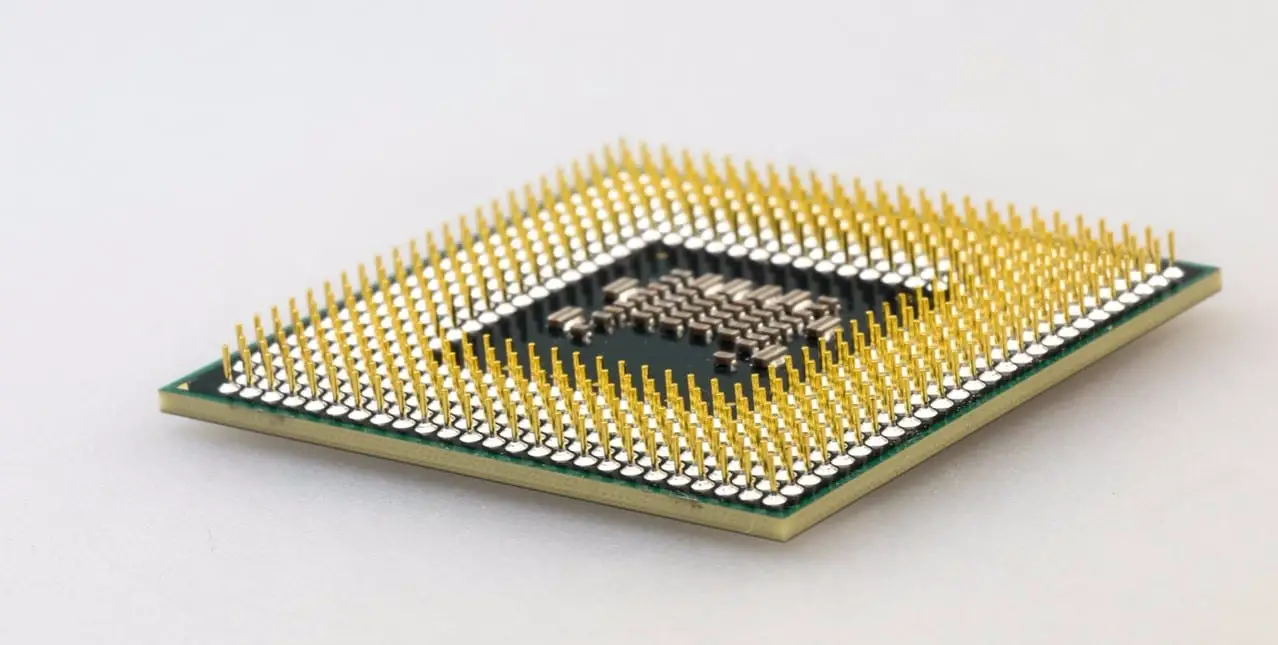
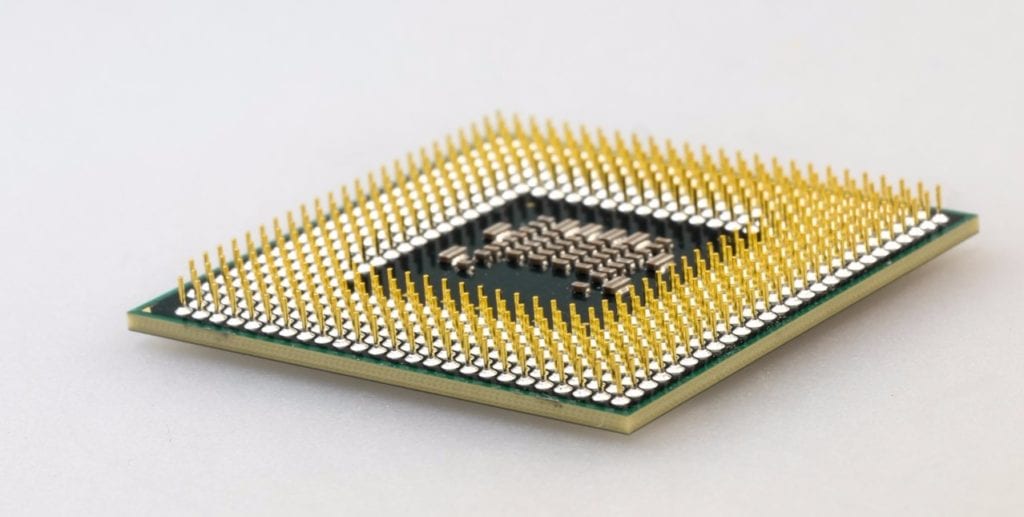
As an overview, both Meltdown and Spectre are bugs at the microprocessor level that allow hackers to gain access to data at the kernel level. As the processes they both exploit are systematic behaviors that have existed at the kernel level for decades, there are vulnerabilities across all major chip makers. As the move towards faster processors and more optimized hardware has been driving forward for many years, these processes have been deployed on chips from Intel, AMD and ARM Holdings at such deep levels that they are not easily patched.
From what I’ve read, both Spectre and Meltdown can’t delete, remove, or overwrite anything: they can, however, steal just about anything that exists on your computer or on servers. Meltdown will be easier to patch for. Spectre will be much, much more difficult, but the exploit is much more difficult for hackers to take advantage of as well.
So there’s that.
These are broad sweeping statements and if you are interested in learning more, I would highly recommend you read articles from The Verge, Ars Technica, The Register and Engadget. My main goal here was to make you aware that a pretty big bug has surfaced and to let you know how your Chromebook fares in all this. Most outlets (understandably so) are focused on Windows and Mac users.
Is Your Chromebook Patched?
There are a couple things you need to know to figure out if your Chromebook is patched against these threats. Google has made it clear on this support page that all Chromebooks will be patched, but there are many that are already taken care of.
First, you need to make sure you have the latest update for Chrome OS. Most users should be on 63, but a few devices are still on 62, including the Pixelbook and Samsung Chromebook Pro/Plus.
Second, you need to know what Kernel your device is running. These exploits are both kernel-level issues, so knowing your kernel number is important. There are a couple ways you can check yours. You can head to this site where they are all listed and can be sorted. Or you can simply type chrome://gpu into your Omnibar. A quick CTRL+F search for “operating system” will show you what Linux kernel you are running.
Systems with kernel 3.18 or 4.4 are already patched. Google’s support page doesn’t clarify if this patches for both Meltdown and Spectre, but based on the articles above, I feel like this will fix the Meltdown issue, but Spectre fixes will come later. Again, there’s nothing specific to that point, so I’m only venturing a guess at this point.
Google also states that ARM-powered Chromebooks are in the clear, here, but they will be patched along with the other kernels in future updates. KTPI (Kernel Page Table Isolation) is the fix being deployed here if you were curious. From The Register’s article above:
The fix is to separate the kernel’s memory completely from user processes using what’s called Kernel Page Table Isolation, or KPTI
So, long story short, most Chromebooks are already patched and the rest will come soon.
Additional Steps
Gabriel wrote a great article in early December that talked about site isolation in Chrome 63. In a nutshell:
Each new event that launches a new page or transcends multiple domains inside an individual tab will all be handled by a new process. This prevents, for example, a malicious malware or highjacker to access multiple pages or exploit extensions.
Because of the new processes in play, RAM usage could potentially be impacted by as much as a 10-20% increase. The good news is that this new feature is disabled by default as it is mainly focused on enterprises that are looking create a more secure infrastructure.
If you want an added layer of exploit security, feel free to enable this feature in Chrome OS 63 by typing in chrome://flags#enable-site-per-process in your Omnibar and selecting Enable.
As stated above, the feature will weigh down your RAM a bit more than Chrome already does, so know this going in.
A Big Fat Mess
Though many Chromebooks are patched and the rest should come in short order, I can’t stress enough the importance of keeping up to date on the development of both Meltdown and Spectre. We are just in the beginning stages of this whole thing and as developers look deeper into the issue, there’s no telling what else will crop up.
My hope? I’m hopeful that as further research is done by gifted and brilliant individuals, a cohesive and permanent fix is found for Intel, AMD, and ARM chips alike. There’s nothing good about any of this. A vulnerability that not only affects our personal devices but also the servers that power so many services we use daily is nothing to be taken lightly.
If I can take one bright spot away, it is this: the fact that Chrome OS was patched extremely quickly for most users and will hopefully be fully complete very soon is a fantastic affirmation that Chrome OS is still king of security among the OS’s on the market.
Leave a Reply
You must be logged in to post a comment.